Menelaus and Meriones lifting Patroclus’ corpse on a cart while Odysseus looks on, Etruscan alabaster urn from Volterra, Italy, 2nd century BC
Between 1500 B.C. and 1200 B.C., Greece was frequently engaged in wars with regional rivals, which led to the development of innovative military and intelligence strategies. The Greeks were masters of deception and intelligence, using cunning and strategic thinking to gain advantages over their enemies.
The Trojan Horse
One of the most renowned examples of Greek cunning and strategic thinking is the legendary incident of the Trojan Horse. According to the myth, Greek soldiers constructed a large wooden horse to infiltrate the city of Troy. Presented as a gift, the horse secretly housed Greek soldiers who emerged at night to open the city gates for the invading army. Whether entirely factual or not, this story underscores the significance of deception and strategic planning in Greek warfare.

Homer’s Works
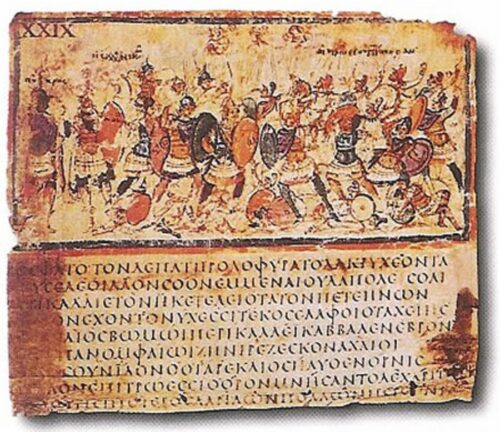
The works of Homer, particularly the Iliad and the Odyssey, provide insights into the espionage practices of ancient Greece. In the Iliad, Odysseus and Diomedes embark on a reconnaissance mission to gather intelligence on the Trojan army’s plans. They capture a Trojan spy named Dolon, who provides valuable information in exchange for his life, though he is ultimately killed by the Greeks. In the Odyssey, Odysseus infiltrates Troy disguised as a house slave to gather intelligence for the Greek forces. These stories illustrate the use of espionage and covert operations in Greek mythology and literature.
Espionage in Greek City-States
In the era of democratic Greek city-states, espionage was a vital political tool. The city-states, such as Athens and Sparta, were in constant competition with each other, and the use of spies was essential to gain an edge over rivals. Espionage allowed city-states to gather critical information about their adversaries, including their military capabilities, defensive structures, and political alliances.
Agents of espionage were tasked with collecting detailed information on the military strength of rival city-states. This included the size of their armies, the types of weapons they used, and their strategic plans. Such intelligence was crucial for preparing defenses and planning military campaigns. For example, knowing the exact number of enemy troops and their positions could help a city-state devise effective counterstrategies.
Understanding the defensive capabilities of rival city-states was another key aspect of espionage. Spies would gather information on fortifications, watchtowers, and other defensive structures. This knowledge was invaluable for planning sieges or surprise attacks. By knowing the weaknesses in an enemy’s defenses, a city-state could exploit these vulnerabilities to gain a tactical advantage.
Espionage also played a significant role in understanding the political landscape. Spies gathered information on the alliances and diplomatic relations between city-states. This intelligence was crucial for forming strategic alliances and making informed decisions about potential conflicts. For instance, knowing which city-states were allied with each other could help in negotiating treaties or planning joint military operations.
The intelligence gathered through espionage was essential for maintaining a balance of power among the Greek city-states. By staying informed about the strengths and weaknesses of their rivals, city-states could make strategic decisions to protect their interests and prevent any single state from becoming too dominant. This balance of power was crucial for the stability and security of the region.

Greek Tradecraft
Greek spies employed a variety of methods to gather intelligence. These included reconnaissance missions, infiltration, and the use of informants.
The Greeks relied heavily on informants to gather intelligence. Informants could be locals, merchants, or even defectors who provided valuable information about enemy plans and movements. Ports and marketplaces were excellent places to gather intelligence, as merchants and travelers brought news from distant locales. Informants played a crucial role in keeping Greek city-states informed about their rivals’ activities.
To protect their communications, the Greeks developed early forms of cryptography. One notable example is the scytale, a tool used by the ancient Greeks, particularly the Spartans, to encrypt messages. The scytale involved wrapping a strip of parchment around a rod to encode messages. Only someone with a rod of the same diameter could decode the message. This method ensured that sensitive information remained secure, even if the message was intercepted.

Final Thoughts
The Greeks’ mastery of deception and intelligence in warfare played a crucial role in their military successes. From the legendary Trojan Horse to the espionage practices depicted in Homer’s works, Greek warfare was characterized by cunning strategies and innovative intelligence methods. The use of spies and cryptographic tools like the scytale highlights the importance of intelligence in maintaining power and achieving victory in ancient Greece.


